A Report about the Visit of KubeCon + CloudNativeCon Europe 2025


A Report about the Visit of KubeCon + CloudNativeCon Europe 2025
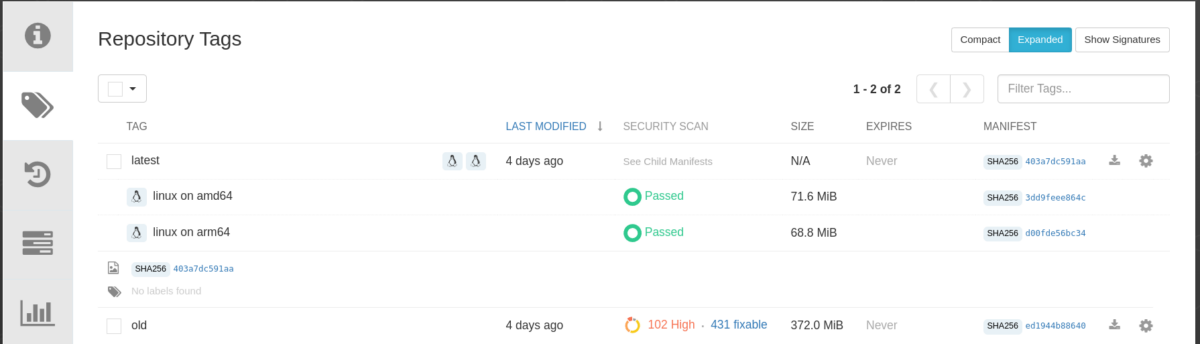
The size of container images plays an essential role in various aspects, not just the amount of storage space used in the Container Registry. In this article, we will explore why optimizing container image size matters and how to achieve it effectively. Oftentimes we have applications whose binaries are quite small but whose container images […]

A Guide to Seamless Connectivity in OpenShift and OKD In today’s rapidly evolving technological landscape, the integration of complex architectures into our systems is becoming more prevalent than ever. One of these challenges is to consolidate a multi-cloud architecture into a true hybrid cloud one. In this blog post we will delve into the motivations, solutions, and considerations […]
Introduction The topic “Denial of Service” (DoS) and “Distributed Denial of Service” (DDoS) is always a hot topic because it could happen at any time for any Service at any Layers. To understand what a (D)DoS is, let us explain what a “service” is, what possible attacks are available and why such a denial of […]
Introduction The topic “Denial of Service” (DoS) and “Distributed Denial of Service” (DDoS) is always a hot topic because it could happen at any time for any Service at any Level. To understand what a (D)DoS is, let us explain what a “Service” is, what possible attacks are available and why such a denial of […]
ˈpætɚns Image source https://vecteezy.com/ Recap In the first article, we discussed the need for patterns as an architectural paradigm, in order to achieve re-usability across complex environments such as Hybrid Cloud scenarios. We identified the benefits of a pattern based approach. We talked about automation, Hybrid Cloud, and about organizational aspects We’ve learned that patterns […]

Photo by Robynne Hu on Unsplash In the perilous realm of digital security, trust is fragile. Transport Layer Security (TLS) web server authentication relies on trust anchors, but a flaw in the design puts web entities at risk of malicious impersonation. This article explores the origin of certificates in the RHEL root trust store and […]
The Problem with Security and Compliance Mixture When talking to customers or colleagues, I often see two distinct topics being conflated: Compliance and (IT-) Security. Some customers have requirements they say MUST be fulfilled. When asked what their goal with this requirement is, they cannot elaborate the intention. They often fall back into saying that […]

Photo by Daniel van den Berg on Unsplash On a warm summer day, I visited the Kubernetes Community Days Munich and enjoyed Adrian Reber’s talk about “Forensic container checkpointing and analysis”. Now I want to try that with OpenShift 4.13! This blog post will mainly cover how to enable and use checkpointing on OpenShift 4.13. […]

Photo by Timelab on Unsplash In this tutorial I will show you how to configure automatic updates for containers in rootless Podman environments and how systemd manages these containers as services. The tutorial is divided into the following sections: If you are not interested in the possible use cases and would rather start right away, […]