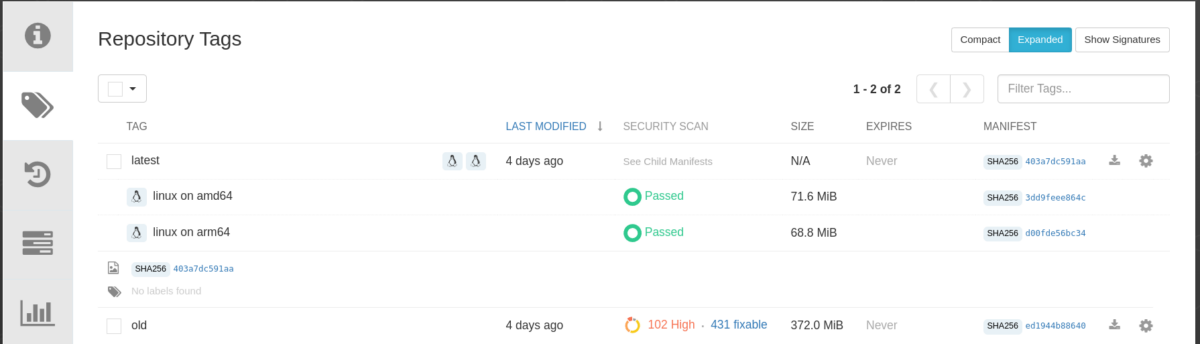
The size of container images plays an essential role in various aspects, not just the amount of storage space used in the Container Registry. In this article, we will explore why optimizing container image size matters and how to achieve it effectively. Oftentimes we have applications whose binaries are quite small but whose container images […]